IIoT × Zero Trust: A new approach to security measures?
Zero trust for all communication access and logs
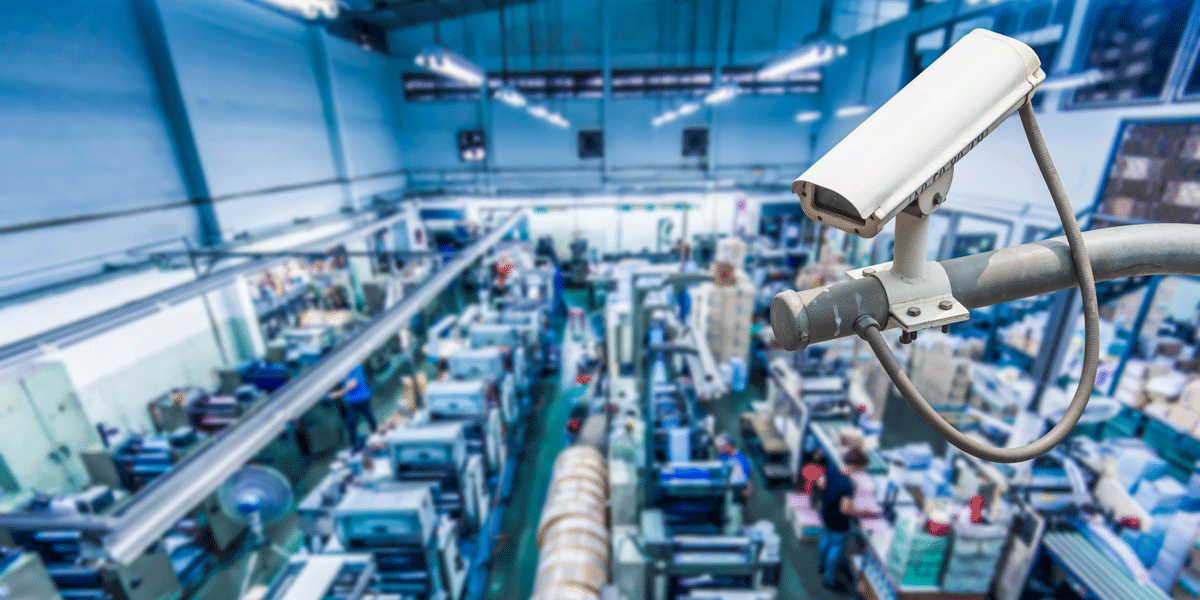
As the Internet of Things (IoT) connects all devices and Digital Transformation (DX) accelerates, the risk of cyberattacks, information leaks, and other issues are increasing. In particular, it is feared that serious damage may occur in the operational technology (OT) systems that operate and control factories and other equipment, such as system destruction or damage, manufacturing line downs, or alteration of control data and parameters. This article explains these security risks along with the new "Zero Trust" approach for security measures.
According to a survey called "Security Measures for IIoT/OT Systems," released in April 2020 by IT specialist research firm IDC Japan, more than 30% of companies in the manufacturing sector such as process assembly and process manufacturing responded that security incidents or accidents have occurred. Also, more than 30% of these companies similarly responded that they have not experienced incidents or accidents but have felt at risk. These incidents and accidents are most common in connections with external networks. The results show an increased risk of cyberattacks due to factories and other production sites connecting internal systems to external networks such as the cloud.
Under these circumstances, the concept of "Zero Trust" is considered a safe system approach for IT networks. "Zero Trust" means abandoning boundary defense models, based on more traditional security principles of "network interiors are secure," and "exterior boundaries should be protected," and instead are taking the approach of a security response on the assumption that all communication access and traffic is untrustworthy.
Traditional IT system security measures have mainly relied on methods such as monitoring network boundaries with firewalls, intrusion detection, and prevention systems (IPS/IDS). On the other hand, in a "Zero Trust" environment, these boundary monitoring-type security measures are considered insufficient. Instead, they measure visualization and verification of all communication access, recording of logs, construction and centralized control of boundaries by software, and boundary management for each device.

Security risks lurking in Smart Factories identified by a demonstration experiment
In collaboration with the Polytechnic University of Milan in Italy, experts in the latest hardware, a leading developer and retailer of computer and internet security products, presented a demonstration of new security risks associated with Smart Factories in May 2020. This demonstration documented risks such as damage to products and production line-downs due to the impact of cyberattacks. It also discovered that manufacturing and design data accumulated by manufacturing execution systems (MES), responsible for managing manufacturing process executions, could be altered. Also, the logic used to operate machine control devices could be changed, forcing the shutdown of production lines or causing other problems.
The main asset is "information" in the IT industry, and preventing its leakage and rewriting is considered a top priority. On the other hand, OT emphasizes "safety" because cyberattacks and other issues may not only cause physical loss, such as machine malfunctions but can also have an impact on human life. It is considered impractical to apply IT security measures "as is" to OT due to the difference in the system architectural approaches between IT and OT. In light of this difference, we continuously investigate Zero Trust for optimized IIoT.
The demonstration results highlighted the risks of software supply chains becoming increasingly complex and showed developers and companies becoming more and more involved as factories become smarter.
The company emphasized the importance of Zero Trust, doubted the security systems of all factory intrusion routes, and implemented measures assuming that invasions would occur. The awareness of these risks is spreading worldwide. In December 2020, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) reported countermeasures against vulnerability in U.S. company-made programs. These programs, widely used in IoT and network-connected devices, could potentially lead to severe damage such as "arbitrary code execution," "denial of service (DoS)," or "out-of-scope memory reading" by attackers.
Moving forward, the question will remain how to construct security risk measures at factories and other production sites. With IoT and DX accelerating, new measures to prevent information and physical losses are necessary.

[PR] Murata Connectivity Modules
Murata connectivity modules are designed to simplify wireless device development and certification by minimizing the amount of RF expertise required to wirelessly enable a wide range of applications.
Click here for details:
https://www.murata.com/en-global/products/connectivitymodule
Related articles
- Technologies and Ideas for Realizing a More Comfortable Society Through Wireless Power Supply (Wireless Power Transfer)
- A Report on Murata Manufacturing's Data Science Case Study Presentations and Corporate Booth - Annual Conference of Japanese Society for Artificial Intelligence, 2024
- Murata Manufacturing Data Scientists Discuss the Power of Practical Application